Internet Explorer 7 Eng Test
Windows11.0.155 (October 8, 2019; 1 day ago ( 2019-10-08) )Mac OS5.2.3 (June 16, 2003; 16 years ago ( 2003-06-16))UNIX5.01 SP1 (2001; 18 years ago ( 2001)),(and previously supported:, ), (and previously supported:, )Included withOSR1 and laterand laterthrough(s),Available in95 languages, a Windows licenseWebsiteInternet Explorer (formerly Microsoft Internet Explorer and Windows Internet Explorer, commonly abbreviated IE or MSIE) is a series of developed by and included in the line of, starting in 1995. It was first released as part of the add-on package that year. Later versions were available as free downloads, or in, and included in the (OEM) service releases of Windows 95 and later versions of Windows. The browser is discontinued, but still.Internet Explorer was once the most widely used web browser, attaining a peak of about 95% by 2003. This came after Microsoft used bundling to win the against, which was the dominant browser in the 1990s. Its usage share has since declined with the launch of (2004) and (2008), and with the growing popularity of operating systems such as and that do not support Internet Explorer. Estimates for Internet Explorer's market share or by StatCounter's numbers ranked 8th, while on desktop, the only platform on which it has ever had significant share (e.g., excluding mobile and ) it is ranked 5th at 4.4%, after its replacement, which at 4.71% that 2019 August month is the first time ranked higher than IE.
IE and Edge manage to reach third rank after Firefox (and previously managed second rank after Chrome) when their (others place IE 3rd with 7.44% after Firefox). Internet Explorer 1The Internet Explorer project was started in the summer of 1994 by, who, according to the Review of 2003, used source code from Mosaic, which was an early commercial web browser with formal ties to the pioneering (NCSA) browser. In late 1994, licensed Spyglass Mosaic for a quarterly fee plus a percentage of Microsoft's non-Windows revenues for the software.
Although bearing a name similar to NCSA Mosaic, Spyglass Mosaic had used the NCSA Mosaic source code sparingly.The first version, dubbed Microsoft Internet Explorer, was installed as part of the Internet Jumpstart Kit in for and Plus! The Internet Explorer team began with about six people in early development. Internet Explorer 1.5 was released several months later for and added support for basic table rendering. By including it free of charge with their, they did not have to pay royalties to Spyglass Inc, resulting in a lawsuit and a 8 million settlement on January 22, 1997.Microsoft was sued by Synet Inc.
In 1996, over the trademark infringement. Internet Explorer 2–10. Main article:Internet Explorer 11 is featured in, which was released on October 17, 2013. It includes an incomplete mechanism for syncing tabs. It is a major update to its, enhanced scaling for high DPI screens, prerender and prefetch, decoding, HTML5 full screen, and is the first Internet Explorer to support and Google's protocol (starting at v3).
This version of IE has features dedicated to Windows 8.1, including cryptography (WebCrypto)and.Internet Explorer 11 was made available for users to download on November 7, 2013, with in the following weeks.Internet Explorer 11's string now identifies the agent as ' (the underlying layout engine) instead of 'MSIE'. It also announces compatibility with (the layout engine of ).Microsoft claimed that Internet Explorer 11, running the WebKit SunSpider JavaScript Benchmark, was the fastest browser as of October 15, 2013.Internet Explorer 11 will be made available for and in the spring of 2019. End of life , officially unveiled on January 21, 2015, has replaced Internet Explorer as the default browser on. Internet Explorer is still installed in Windows 10 in order to maintain compatibility with older websites and sites that require and other Microsoft legacy web technologies.According to Microsoft, development of new features for Internet Explorer has ceased.
However, it will continue to be as part of the support policy for the versions of Windows with which it is included. Features. As seen inInternet Explorer has been designed to view a broad range of web pages and provide certain features within the operating system, including.
During the heyday of the, Internet Explorer superseded only when it caught up technologically to support the progressive features of the time. Standards support Internet Explorer, using the:. Supports 4.01, parts of, Level 1, Level 2 and Level 3, 1.0, and Level 1, with minor implementation gaps.
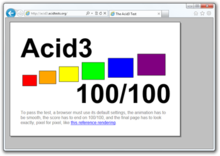
Fully supports 1.0 as well as an obsolete Microsoft dialect of XSLT often referred to as WD-xsl, which was loosely based on the December 1998 W3C Working Draft of. Support for lies in the future: semi-official Microsoft bloggers have indicated that development is underway, but no dates have been announced. Almost full conformance to CSS 2.1 has been added in the release. The trident rendering engine in Internet Explorer 9 in 2011, scored highest in the of all major browsers. Supports in ( version 5.0). Prior versions can render XHTML documents authored with HTML compatibility principles and served with a text/html.
Supports a subset of in ( version 5.0), excluding SMIL, SVG fonts and filters.Internet Explorer uses to choose between standards mode and a ' in which it deliberately mimicks nonstandard behaviours of old versions of MSIE for HTML and CSS rendering on screen (Internet Explorer always uses standards mode for printing). It also provides its own dialect of called.Internet Explorer was criticised by for its limited support for, which is promoted. Non-standard extensions Internet Explorer has introduced an array of proprietary extensions to many of the standards, including HTML, CSS, and the DOM. Main articles: andInternet Explorer caches visited content in the folder to allow quicker access (or offline access) to previously visited pages.
Internet Explorer 7 Eng Test 1
The content is indexed in a database file, known as. Multiple files exist which index different content—visited content, visited, cookies, etc.Prior to IE7, clearing the cache used to clear the index but the files themselves were not reliably removed, posing a potential security and privacy risk. In IE7 and later, when the cache is cleared, the cache files are more reliably removed, and the index.dat file is overwritten with null bytes.Caching has been improved in IE9. Group Policy.
Main article:Internet Explorer is fully configurable using. Administrators of (for domain-joined computers) or the local computer can apply and enforce a variety of settings on computers that affect the user interface (such as disabling menu items and individual configuration options), as well as underlying security features such as downloading of files, zone configuration, per-site settings, ActiveX control behaviour and others. Policy settings can be configured for each user and for each machine. Internet Explorer also supports.Architecture. The architecture of IE8. Previous versions had a similar architecture, except that both tabs and the UI were within the same process. Consequently, each browser window could have only one 'tab process'.Internet Explorer uses a architecture built on the (COM) technology.
It consists of several major components, each of which is contained in a separate (DLL) and exposes a set of COM hosted by the Internet Explorer main executable, iexplore.exe:. WinInet.dll is the protocol handler for,. It handles all network communication over these protocols. URLMon.dll is responsible for -type handling and download of web content, and provides a thread-safe wrapper around WinInet.dll and other protocol implementations. MSHTML.dll houses the introduced in, which is responsible for displaying the pages on-screen and handling the of the web pages. MSHTML.dll parses the HTML/CSS file and creates the internal tree representation of it. It also exposes a set of for runtime inspection and modification of the DOM tree.
The DOM tree is further processed by a layout engine which then renders the internal representation on screen. IEFrame.dll contains the user interface and window of IE in Internet Explorer 7 and above. ShDocVw.dll provides the navigation, local caching and history functionalities for the browser.
BrowseUI.dll is responsible for rendering the browser user interface such as menus and toolbars.Internet Explorer does not include any native scripting functionality. Rather, MSHTML.dll exposes an API that permits a programmer to develop a scripting environment to be plugged-in and to access the DOM tree. Internet Explorer 8 includes the bindings for the engine, which is a part of and allows any language implemented as an Active Scripting module to be used for client-side scripting. By default, only the and modules are provided; third party implementations like (for support) can also be used.
Microsoft also makes available the runtime (not supported in ) that allows, including -based dynamic languages like and, to be used for client-side scripting.introduces some major architectural changes, called Loosely Coupled IE (LCIE). LCIE separates the main window process (frame process) from the processes hosting the different web applications in different tabs (tab processes). A frame process can create multiple tab processes, each of which can be of a different; each tab process can host multiple web sites. The processes use asynchronous to synchronize themselves. Generally, there will be a single frame process for all web sites. In with Protected Mode turned on, however, opening privileged content (such as local HTML pages) will create a new tab process as it will not be constrained by Protected Mode.

Extensibility. See also: andInternet Explorer exposes a set of (COM) interfaces that allows to extend the functionality of the browser. Extensibility is divided into two types: Browser extensibility and content extensibility.
Browser extensibility involves adding context menu entries, toolbars, menu items or (BHO). BHOs are used to extend the feature set of the browser, whereas the other extensibility options are used to expose that feature in the user interface. Content extensibility adds support for non-native content formats.
It allows Internet Explorer to handle new and new, e.g. In addition, web pages can integrate known as controls which run on Windows only but have vast potentials to extend the content capabilities; and are examples. Add-ons can be installed either locally, or directly by a web site.Since malicious add-ons can compromise the security of a system, Internet Explorer implements several safeguards. Internet Explorer 6 with Service Pack 2 and later feature an Add-on Manager for enabling or disabling individual add-ons, complemented by a 'No Add-Ons' mode., Internet Explorer and its BHOs run with restricted privileges and are isolated from the rest of the system. Internet Explorer 9 introduced a new component – Add-on Performance Advisor. Add-on Performance Advisor shows a notification when one or more of installed add-ons exceed a pre-set performance threshold.
The notification appears in the Notification Bar when the user launches the browser. Windows 8 and introduce a of Internet Explorer that is entirely sandboxed and does not run add-ons at all. In addition, Windows RT cannot download or install ActiveX controls at all; although existing ones bundled with Windows RT still run in the traditional version of Internet Explorer.Internet Explorer itself can be hosted by other applications via a set of COM interfaces. This can be used to embed the browser functionality inside a computer program or create. Security. See also:Internet Explorer uses a zone-based framework that groups sites based on certain conditions, including whether it is an Internet- or intranet-based site as well as a user-editable whitelist. Security restrictions are applied per zone; all the sites in a zone are subject to the restrictions.Internet Explorer 6 SP2 onwards uses the Attachment Execution Service of to mark executable files downloaded from the Internet as being potentially unsafe.
Accessing files marked as such will prompt the user to make an explicit trust decision to execute the file, as executables originating from the Internet can be potentially unsafe. This helps in preventing accidental installation of malware.Internet Explorer 7 introduced the phishing filter, that restricts access to sites unless the user overrides the decision.
With version 8, it also blocks access to sites known to host. Downloads are also checked to see if they are known to be malware-infected.In, Internet Explorer by default runs in what is called Protected Mode, where the privileges of the browser itself are severely restricted—it cannot make any system-wide changes.
One can optionally turn this mode off but this is not recommended. This also effectively restricts the privileges of any add-ons. As a result, even if the browser or any add-on is compromised, the damage the security breach can cause is limited.Patches and updates to the browser are released periodically and made available through the Windows Update service, as well as through.
Although security patches continue to be released for a range of platforms, most feature additions and security infrastructure improvements are only made available on operating systems which are in Microsoft's mainstream support phase.On December 16, 2008, recommended users switch to rival browsers until an emergency patch was released to fix a potential security risk which 'could allow outside users to take control of a person's computer and steal their passwords'. Microsoft representatives countered this recommendation, claiming that '0.02% of internet sites' were affected by the flaw. A fix for the issue was released the following day with the Security Update for Internet Explorer KB960714, on Microsoft Windows Update.In 2011, a report by Accuvant, funded by Google, rated the security (based on sandboxing) of Internet Explorer worse than but better than.A more recent browser security white paper comparing, and by X41 D-Sec in 2017 came to similar conclusions, also based on sandboxing and support of legacy web technologies. Security vulnerabilities. See also:Internet Explorer has been subjected to many security vulnerabilities and concerns: much of the, and across the Internet are made possible by exploitable bugs and flaws in the security architecture of Internet Explorer, sometimes requiring nothing more than viewing of a malicious web page in order to install themselves. This is known as a '.
There are also attempts to trick the user into installing malicious software by misrepresenting the software's true purpose in the description section of an security alert.A number of security flaws affecting IE originated not in the browser itself, but -based add-ons used by it. Because the add-ons have the same privilege as IE, the flaws can be as critical as browser flaws.
This has led to the ActiveX-based architecture being criticized for being fault-prone. By 2005, some experts maintained that the dangers of ActiveX have been overstated and there were safeguards in place. In 2006, new techniques using found more than a hundred vulnerabilities in standard Microsoft ActiveX components.
Security features introduced in Internet Explorer 7 mitigated some of these vulnerabilities.In 2008, Internet Explorer had a number of published security vulnerabilities. According to research done by security research firm, Microsoft did not respond as quickly as its competitors in fixing security holes and making patches available. The firm also reported 366 vulnerabilities in ActiveX controls, an increase from the previous year.According to an October 2010 report in, researcher Chris Evans had detected a known security vulnerability which, then dating back to 2008, had not been fixed for at least 600 days. Microsoft says that it had known about this vulnerability but it was of very low severity as the victim web site must be configured in a special way for this attack to be feasible at all.In December 2010, researchers were able to bypass the 'Protected Mode' feature in Internet Explorer.
Vulnerability exploited in attacks on U.S. Browser market share worldwide, July 2017In an advisory on January 14, 2010, Microsoft said that attackers targeting Google and other U.S.
Companies used software that exploits a security hole, which had already been patched, in Internet Explorer. The vulnerability affected Internet Explorer 6 on Windows XP and Server 2003, IE6 SP1 on Windows 2000 SP4, IE7 on Windows Vista, XP, Server 2008 and Server 2003, and IE8 on Windows 7, Vista, XP, Server 2003, and Server 2008 (R2).The warned users against using Internet Explorer and recommended switching to an alternative web browser, due to the major security hole described above that was. The Australian and French Government issued a similar warning a few days later. Major vulnerability across versions On April 26, 2014, Microsoft issued a security advisory relating to CVE-2014-1776 (use-after-free vulnerability in Microsoft Internet Explorer 6 through 11 ), a vulnerability that could allow 'remote code execution' in Internet Explorer versions 6 to 11. On April 28, 2014, the United States 's (US-CERT) released an advisory stating that the vulnerability could result in 'the complete compromise' of an affected system.
US-CERT recommended reviewing Microsoft's suggestions to mitigate an attack or using an alternate browser until the bug is fixed. The UK National Computer Emergency Response Team (CERT-UK) published an advisory announcing similar concerns and for users to take the additional step of ensuring their antivirus software is up-to-date., a cyber security firm, confirmed that 'the vulnerability crashes Internet Explorer on Windows XP'. The vulnerability was resolved on May 1, 2014, with a security update.
Market adoption and usage share. Historical market share of Internet ExplorerThe adoption rate of Internet Explorer seems to be closely related to that of Microsoft Windows, as it is the default web browser that comes with Windows. Since the integration of Internet Explorer 2.0 with Windows 95 OSR 1 in 1996, and especially after version 4.0's release in 1997, the adoption was greatly accelerated: from below 20% in 1996, to about 40% in 1998, and over 80% in 2000. This made Microsoft the winner in the infamous ' against. Was the dominant browser during 1995 and until 1997, but rapidly lost share to IE starting in 1998, and eventually slipped behind in 1999. The integration of IE with Windows led to a lawsuit by, Netscape's owner, accusing Microsoft of unfair competition. The infamous case was eventually won by AOL but by then it was too late, as Internet Explorer had already become the dominant browser.Internet Explorer peaked during 2002 and 2003, with about 95% share.
Its first notable competitor after beating Netscape was from, which itself was an offshoot from Netscape.Firefox 1.0 had surpassed in early 2005, with Firefox 1.0 at roughly 8 percent market share.Approximate usage over time based on various usage share counters averaged for the year overall, or for the fourth quarter, or for the last month in the year depending on availability of reference.According to StatCounter Internet Explorer's marketshare fell below 50% in September 2010. In May 2012, overtook Internet Explorer as the most used browser worldwide, according to StatCounter. Industry adoption are also used by many companies and third parties for creating add-ons that access their services, such as search engine toolbars. Because of the use of COM, it is possible to embed web-browsing functionality in third-party applications. Hence, there are a number of, and a number of content-centric applications like also use Internet Explorer's web browsing module for viewing web pages within the applications.Removal. Main article:While a major upgrade of Internet Explorer can be uninstalled in a traditional way if the user has saved the original application files for installation, the matter of uninstalling the version of the browser that has shipped with an operating system remains a controversial one.The idea of removing a stock install of Internet Explorer from a Windows system was proposed during the case. One of Microsoft's arguments during the trial was that removing Internet Explorer from Windows may result in system instability.
Indeed, programs that depend on libraries installed by IE, including Windows help and support system, fail to function without IE. Before, it was not possible to run without IE because the service used technology, which no other web browser supports.Impersonation by malware The popularity of Internet Explorer has led to the appearance of malware abusing its name. On January 28, 2011, a fake Internet Explorer browser calling itself 'Internet Explorer – Emergency Mode' appeared. It closely resembles the real Internet Explorer, but has fewer buttons and no search bar. If a user attempts to launch any other browser such as, or the real Internet Explorer, this browser will be loaded instead. It also displays a fake error message, claiming that the computer is infected with malware and Internet Explorer has entered 'Emergency Mode'.
It blocks access to legitimate sites such as if the user tries to access them. See also. Support (18 ed.).
October 8, 2019. Retrieved July 27, 2013. ^. Microsoft Edge Development.
Archived from on July 16, 2016. The latest features and platform updates will only be available in Microsoft Edge.
We will continue to deliver security updates to Internet Explorer 11 through its supported lifespan. To ensure consistent behavior across Windows versions, we will evaluate Internet Explorer 11 bugs for servicing on a case by case basis.
StatCounter Global Stats. Retrieved September 6, 2019. Retrieved May 2, 2019. Retrieved October 17, 2008.
Retrieved February 6, 2015. Paul Maritz. Retrieved February 6, 2015. There is talk about how we get more $'s from the 1000+ people we have working on browser related stuff. Retrieved March 13, 2019.
Retrieved March 13, 2019. Retrieved July 12, 2018.
March 17, 2015. Retrieved March 18, 2015.
Retrieved September 21, 2019. March 31, 2016. Compared with older versions of Internet Explorer, Internet Explorer 11 offers improved security. Microsofts's MSDN blog. August 7, 2014. Retrieved August 29, 2014. Retrieved March 18, 2015.
Rotten Websites Wiki. Retrieved August 12, 2018. MIT Technology Review. Retrieved January 18, 2015. ^ Elstrom, Peter (January 22, 1997). Archived from on June 29, 1997.
Retrieved February 9, 2011. ^ (January 22, 1997). Archived from on September 19, 2012. Retrieved February 9, 2011. ^. Retrieved October 17, 2008.
at the (archived 2005-10-01). Borland, John (April 15, 2003). Retrieved February 9, 2011. (January 22, 1997). Archived from on September 19, 2012. Retrieved February 9, 2011. Goodwins, Rupert (August 15, 1996).
Archived from on December 5, 2011. Retrieved April 20, 2019. ^ Thurrott, Paul (July 25, 2013). Paul Thurrott's SuperSite for Windows. Retrieved July 26, 2013. June 26, 2013. Retrieved July 13, 2013.
July 25, 2013. Retrieved July 26, 2013.
July 25, 2013. Retrieved July 26, 2013. Bradley, Tony (July 26, 2013). Retrieved July 27, 2013. ^ Brinkmann, Martin (July 25, 2013).
Ghacks Technology News. Retrieved July 27, 2013. Retrieved May 29, 2013. Retrieved May 29, 2013. July 25, 2013. Retrieved July 26, 2013.
Lardinois, Frederic (June 26, 2013). Retrieved September 10, 2013. Williams, Mike (July 26, 2013). BetaNews, Inc. Retrieved July 27, 2013. Retrieved November 8, 2013.
Retrieved October 23, 2013. January 28, 2019. Retrieved March 26, 2019. Weber, Jason (January 21, 2015). IEBlog. Rossi, Jacob (November 11, 2014). IEBlog.
Warren, Tom (January 27, 2015). Brian wilson. Retrieved September 26, 2010. Retrieved March 11, 2008. Hopkins, James. Archived from on August 1, 2009. Retrieved April 15, 2011.
Svensson, Peter (September 10, 2008). Archived from on December 19, 2008. Retrieved November 16, 2008. Schiller, Jeff. Retrieved April 20, 2019.
May 12, 2005. Microsoft Docs. October 24, 2011. Retrieved April 20, 2019. Microsoft Typography. February 26, 2001. Archived from on April 28, 2005.
Retrieved April 20, 2019. Archived from on December 17, 2008.
Retrieved April 20, 2019. Davis, Jeff (December 27, 2007).
Jeffdav on code. Retrieved March 11, 2013. September 7, 2013. Retrieved April 20, 2019. Windows Core Networking Team (August 4, 2006). Archived from on January 12, 2008.
Retrieved April 20, 2019. March 17, 2011. Retrieved April 20, 2019. ^.
Retrieved January 10, 2007. Wilson, Chris. MSDN Channel9. Retrieved March 7, 2008.
Zeigler, Andy (March 11, 2008). Retrieved April 20, 2019. ^ McSherry, Tony (January 20, 2013).
December 16, 2008. December 16, 2008. Retrieved May 5, 2010. Goodin, Dan (December 9, 2011). The Register. Retrieved October 15, 2012. ESecurity Planet.
December 13, 2011. Retrieved May 22, 2012.
(PDF). X41-Dsec GmbH. September 18, 2017. Retrieved September 21, 2017. Seltzer, Larry (April 14, 2005).
Retrieved April 7, 2006. Lemos, Robert (July 31, 2006). Security Focus. Retrieved July 11, 2009.
(PDF). Secunia. Goodin, Dan (November 1, 2010). The Register. Retrieved November 2, 2010.
Naraine, Ryan (November 1, 2010). Retrieved November 2, 2010. December 3, 2010. Retrieved December 4, 2010. Retrieved August 2, 2017.
Mills, Elinor (January 14, 2010). Retrieved September 26, 2010. Emery, Daniel (January 16, 2010).
Retrieved March 26, 2010. Fildes, Jonathan (January 18, 2010). Retrieved March 26, 2010. Emily Bourke for AM (January 19, 2010). Retrieved September 26, 2010. Martinez-Cabrera, Alejandro (January 18, 2010).
The San Francisco Chronicle. Govan, Fiona (January 18, 2010). The Daily Telegraph. Retrieved March 26, 2010. Common Vulnerabilities and Exposures (CVE). January 29, 2014. Retrieved May 16, 2017.
April 26, 2014. Retrieved April 28, 2014. Finkle, Jim (April 28, 2014).
Retrieved April 28, 2014. United States Computer Emergency Readiness Team. April 28, 2014. Retrieved April 28, 2014. Carnegie Mellon University. April 27, 2014.

Retrieved April 28, 2014. Chicago Tribune. April 28, 2014. Retrieved April 28, 2014. April 28, 2014. Retrieved April 28, 2014. Microsoft Technet.
Retrieved July 6, 2014. Retrieved February 9, 2011. Borland, John., ZDNet, April 15, 2003. Accessed June 2, 2012. Archived from on October 3, 2008.
Retrieved October 17, 2008. Archived from on October 2, 2008. Retrieved October 17, 2008. Archived from on August 16, 2000. Retrieved October 17, 2008.
Archived from on April 20, 2008. Retrieved October 17, 2008. Goldman, David (October 6, 2010). Retrieved October 6, 2010. May 21, 2012. Retrieved January 19, 2019. January 28, 2011.
From the original on June 30, 2011. Retrieved June 23, 2013.
January 28, 2011. Retrieved June 23, 2013.Further reading. Browser History: Windows Internet Explorer.
Retrieved December 22, 2013. (July 27, 2005). Retrieved December 22, 2013. Wilson, Chris (July 30, 2005).
Retrieved December 22, 2013. Graff, Scott (October 7, 2006). Retrieved December 22, 2013. March 1, 2005. Retrieved December 22, 2013. News Center. February 15, 2005.
Retrieved December 22, 2013. Williams, Mary-Lynne; MacNeil, Leslie; Hall, Marty (September 17, 2010). Retrieved December 22, 2013.External links Wikimedia Commons has media related to.Wikinews has related news:Wikibooks has a book on the topic of:.